Which of the Following Best Describes a Rootkit
A destructive program disguised as a real program such as a screensaver. Which of the following best describes a vulnerability.

Pdf Unix And Linux Based Rootkits Techniques And Countermeasures
C A program that easily can hide and allow someone to take full control of your computer from a remote location.

. Which of the following best describes a rootkit. Replicates itself over a network to infect computers and devices. Software that reports data such as surfing habits and sites visited.
Software used for the collection of personal data. A destructive program disguised as a real program such as a screensaver. AA virus that changes its code as it delivers the infection.
Which of the following is any event or action that could cause a loss of or damage to computer hardware software data information or processing capability. A virus that changes its code as it delivers the infection. C The intent to reform.
Which of the following best describes a rootkit. A hardware device that reinforces security settings on a computer or network A program that hides in a computer or mobile device and allows. Replicates itself over a network to infect computers and devices.
Which of the folowing are characteristics of a rootkit Select two. Computer viruses worms Trojan horses and rootkits are classified as which of the following. The program then tracks system activity and allows an attacker to remotely gain administrator access to the computer.
Avirus bbackdoor cweakness drootkit. D A lack of fear of being caught. Which of the following best describes spyware.
Which of the following best describes a rootkit. Chapter 1 - Hacking. Software used for the collection of personal data.
Which of the following best describes a rootkit. A program that easily can hide and allow someone to take full. At which layer of the OSI model does a proxy operate.
The Correct Answer is- D. A rootkit is a collection of computer software typically malicious designed to enable access to a computer or an area of its software that is not otherwise allowed for example to an unauthorized user and often masks its existence or the existence of other software. A virus that changes its code as it delivers the infection.
A rootkit is a collection of tools programs that enable administrator-level access to a computer or computer network. B A desire to be helpful. Which of the following is also known as ZeroAccess and has virus Trojan horse and rootkit components.
Which of the terms best describes this software. Which of the following term best describes this software. When users run the software it installs itself as a hidden program that has administrator access to various operating system components.
Which of the following best describes a rootkit. Jerry runs a tool to scan a clean system to create a database. Which of the following best describes a vulnerability.
A Physical B Network C Data Link D. A A disregard for the law. The program then tracks system activity and allows an attacker to remotely gain administrator access to the computer.
The tool then scans the system again and compares the second scan to the clean database. Software hidden on a computer for the purpose of compromising the system. Software that reports data such as surfing habits and sites visited 5.
ARootkit BBotnet CTrojan. Software that provides the originator with the venue to propagate. Which of the following terms best describes this software.
MGMT FINAL 9 35 terms. Software hidden on a computer for the purpose of compromising the system. Passphrase When a botnet is used to attack computers or networks it is called an DoS attack Select one enterprise distributed devastating organized Which of the following best describes a rootkit.
Review Questions Chapter3 20 terms. Which of the following best describes a rootkit. When users run the software it installs itself as a hidden program that has administrator access to various operating system components.
Software that provides the originator with the venue to propagate. Typically a cracker installs a rootkit on a computer after first obtaining user-level access either by exploiting a known vulnerability or cracking a password. Which of the following best describes the term cybercrime.
BReplicates itself over a network to infect computers and devices. It monitors the actions you take on your machine and sends. Which of the following best describes a vulnerability.
D A rootkit Show Answer The Correct Answer is- C 1. The Next Generation 87 terms.
Pdf Countering Persistent Kernel Rootkits Through Systematic Hook Discovery

How To Keep Your Iphone Or Ipad Malware Free Internet Security Network Tools Mcafee
Ccna Cyber Ops Version 1 1 Chapter 6 Exam Answers Full

How To Install Rkhunter For Rootkit Trojan Scanning Trojan Installation Retail Logos

Threats Malware Threats Protect Against Online Types Found Types Need You Of Of Totypes O Computer Security Cyber Security Awareness Cyber Threat

Ruby Vs Python Which Is Better Ruby On Rails Or Python And Django This Is A Question We Get Asked Repeatedly It Learn Web Development Learn To Code Python
Lab 5 Rootkits Backdoors And Trojans

Pdf Windows Rootkits Attacks And Countermeasures

Determining Malware Types Get Certified Get Ahead

Rootkits How Can You Protect Yourself Against Them Ionos
Rootkits For Dummies Larry Stevenson Nancy Altholz 9780471917106 Amazon Com Books
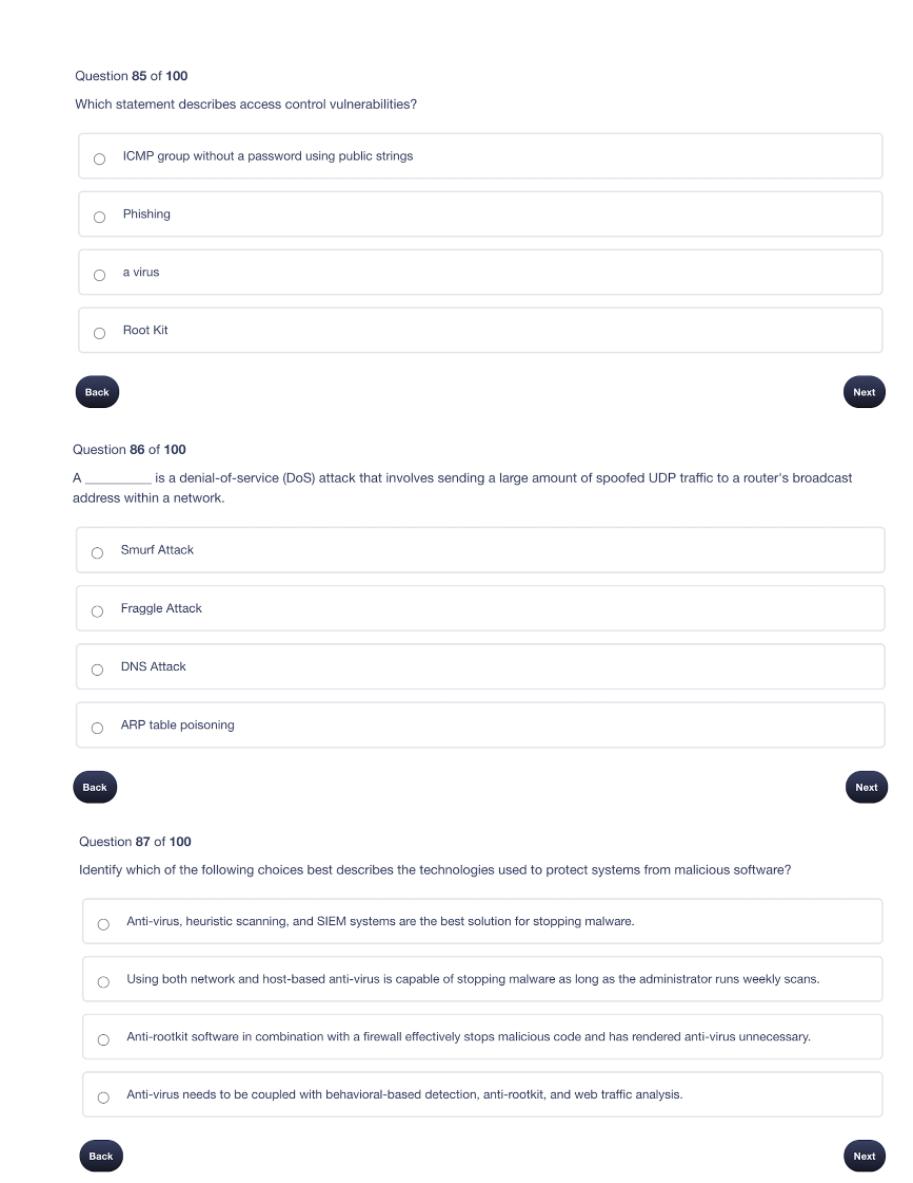
Solved Question 85 Of 100 Which Statement Describes Access Chegg Com

Top 1000 Passwords Password Cracking Passwords Online Security

Pin On Mcafee Antivirus Customer Service Number Mcafee Not Working Scan

Pin By Dean Neumann On Computers Gmail Webmail Cpanel

Mailmatters Control Your Inbox How To Stop Emails Spam Yahoo Hotmail Gmail Sending Server Outlook Express Outlook Software
Github Rounndel Anti Rootkit Lkm A Simple Anti Rootkit Linux Kernel Module For An Operating Systems Security Course

How To Safeguard Yourself Against Ransomware Like Bad Rabbit Tech Help Helpful Supportive

Comments
Post a Comment